Every business relies on information. Customer and employee data, financial records, and supplier contracts are all examples of information whose disclosure or loss could expose an organisation to financial damage or legal liability. Protecting that information requires a clear set of rules, and that is precisely what an information security policy provides.
What Is an Information Security Policy?
An information security policy defines what an organisation needs to protect and to what standard. It applies to everyone who handles the organisation’s information assets, whether they are employees, senior managers, or external suppliers.
Operational procedures and technical guidelines should align with the policy. It sets the framework within which IT teams and asset owners make decisions about security configurations or encryption standards. The policy also has a communication role: it tells everyone in the organisation exactly what is expected of them when handling data.
Documenting an information security policy is also the first step in building an information security management system (ISMS). The policy sets the direction for the remaining elements of the system, such as risk assessments and incident response procedures. Once approved, it ensures that these elements work together and that decisions are made on a consistent basis.
Why an Information Security Policy Matters
Many organisations protect their data to some extent, but without a single document that sets out shared rules. IT implements technical controls, legal teams focus on regulatory compliance, and management makes budget decisions. When each department follows its own approach, gaps and inconsistencies are inevitable. An information security policy brings these efforts together by giving the entire organisation a common point of reference.
The policy also carries weight externally. Clients and partners increasingly ask about formal information security arrangements before entering into a business relationship. Auditors and regulators treat an approved policy as a baseline for assessing compliance. Organisations that have one in place find it easier to build trust with business partners and move through audits more smoothly.
The Regulatory Basis for an Information Security Policy
Several major regulations require or strongly encourage organisations to maintain a formal information security policy.
- ISO 27001
An information security policy is one of the requirements of ISO 27001. It is therefore a prerequisite for certification and a key element of any ISMS. - GDPR
The EU General Data Protection Regulation (GDPR) requires data controllers to implement appropriate technical and organisational measures to protect personal data. An information security policy helps structure those measures and makes it easier to demonstrate compliance to a supervisory authority. Organisations subject to the UK GDPR face equivalent obligations. - NIS2
The EU NIS2 Directive requires essential and important entities to implement cybersecurity risk management measures, including a documented security policy. Organisations that have already built an ISMS in line with ISO 27001 have a head start here, as their policy and supporting procedures are already in place.
Key Elements of an Information Security Policy
Every information security policy needs a few core elements to be effective.
Scope comes first. The policy should specify which systems and business processes it covers, and whether it extends to areas like remote working or third-party access to the organisation’s resources. It should also define key terms, such as security incident or information asset owner, so that readers interpret them consistently.
Before choosing specific controls, an organisation should take stock of its information assets and the context in which it operates. What data does it hold? Where is it stored? Who has access? This analysis reveals which resources matter most to the business and helps the policy focus protection where it is needed most.
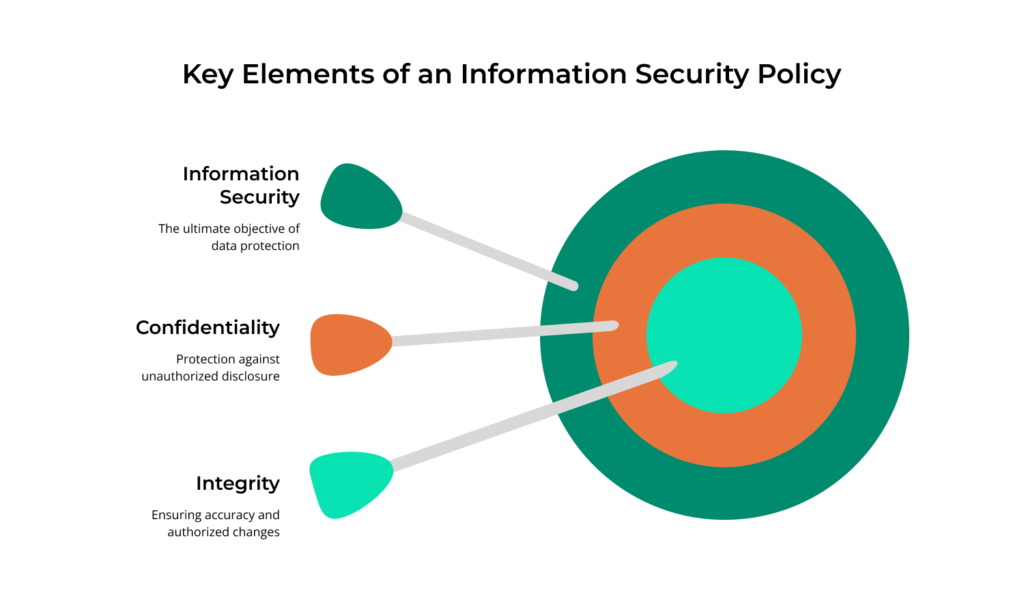
Policy objectives should align with the CIA model: confidentiality, integrity, and availability. Confidentiality means protecting information from disclosure to anyone who should not have access to it. Integrity ensures that data remains accurate and unaltered unless a change is properly approved. Availability ensures that the right people can reach the information they need, when they need it. To be useful, these objectives should be measurable and specific enough to verify. A good example is setting a maximum acceptable downtime for critical systems.
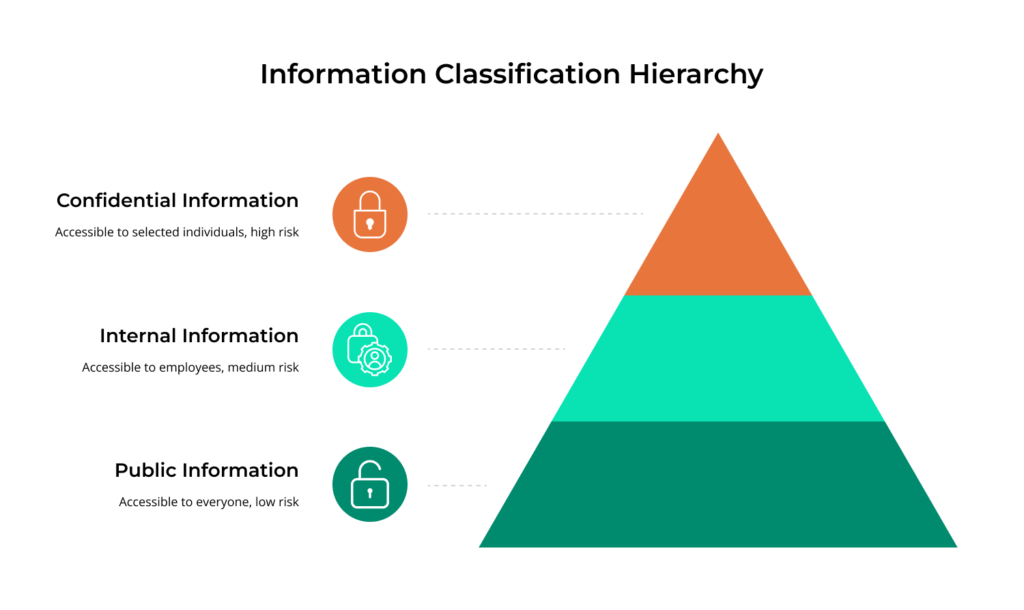
Information classification is another essential element. The organisation should define classification levels, for instance public, internal, and confidential, and assign handling and access rules to each. Classification feeds into risk assessment: the more sensitive the data, the greater the impact of a breach and the tighter the controls need to be.
The policy should also cover roles and responsibilities, access management, and incident response. We address each of these in the sections that follow.
Roles and Responsibilities
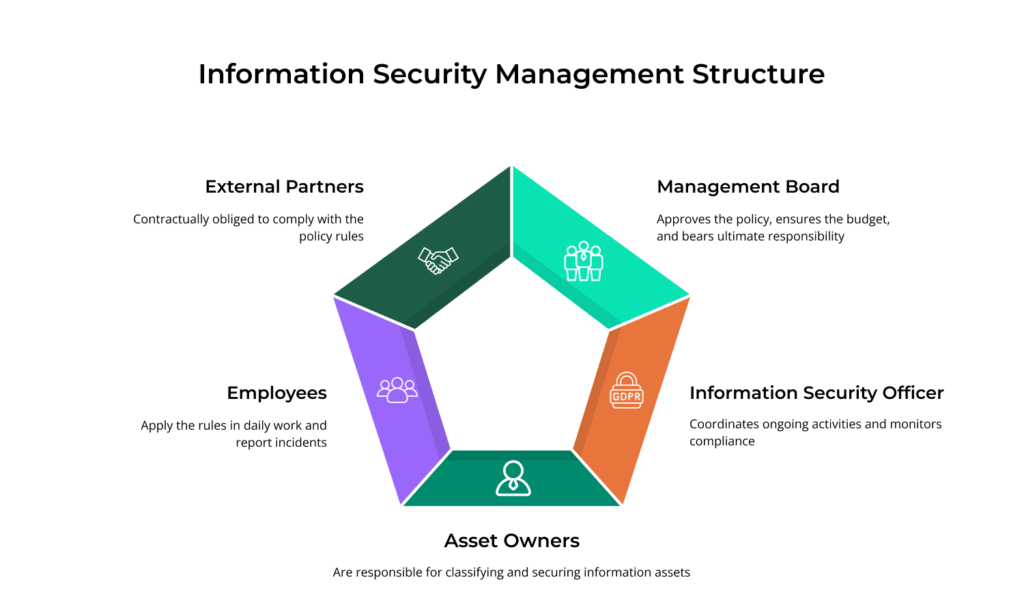
A clear division of roles is essential for any information security policy to work. Everyone in the organisation needs to know what is expected of them.
The board approves the policy, provides the budget to implement it, and is ultimately accountable for information security. Under ISO 27001, active involvement from senior leadership is a formal requirement. Day-to-day coordination typically sits with an information security officer or CISO, who monitors compliance and reports to management on the state of data protection. Asset owners are responsible for classifying the information in their care and applying appropriate controls.
The policy extends to employees and external partners alike. Employees follow its rules in their daily work and report suspected incidents. Suppliers and contractors should be contractually required to comply with the policy wherever they handle the organisation’s data. If these roles are not spelled out in the document, accountability gaps quickly emerge and no one takes ownership.
Access Management and Data Protection
Access control is central to information security, and the policy should set out the ground rules.
The principle of least privilege is a good place to start. Every user should only have the access they need to do their job. The policy should also cover logical controls such as identity verification and permission management. Physical controls matter too, for example restricting entry to server rooms or archives. Access rights need regular review so that outdated permissions do not go unnoticed.
If the organisation processes personal data, the policy should reference the relevant data protection framework, be it the EU GDPR, the UK GDPR, or both. Alternatively, it can point to a dedicated data protection policy. Rules on encryption and data backups are also worth including.
Incident Response
No organisation can eliminate every threat. The policy should therefore set out what happens when something goes wrong.
At a minimum, it should require staff to report security incidents and make clear who receives those reports. It should also outline the general response steps, starting with an assessment of severity and prompt notification of the right people. A detailed incident response plan is typically a separate ISMS document, but it takes its direction from the policy.
The EU NIS2 Directive requires essential and important entities to report significant incidents to the relevant CSIRT (Computer Security Incident Response Team) within set deadlines. The policy should reflect these obligations and identify who is responsible for liaising with supervisory authorities. When response procedures are poorly defined, reaction times suffer and the damage grows.
Reviewing and Updating the Policy
An information security policy that is never updated will eventually drift out of step with the organisation it is meant to protect. Regular reviews keep the document aligned with current threats and legal requirements.
A review should take place at least once a year, and sooner after any significant change, such as a restructuring, a shift in risk profile, or new legislation. There should be clear rules about who initiates the review (typically the information security officer or CISO), who approves changes (senior management), and how the revision history is recorded.
Internal audits play a different but equally important role. They check whether the policy is being followed and whether its provisions still reflect conditions on the ground. Findings highlight gaps and feed directly into the next review cycle.
In an information security management system built around ISO 27001, policy updates form part of the PDCA cycle (Plan-Do-Check-Act). The organisation plans its controls, implements them, checks how well they work, and makes corrections. The policy lives alongside this cycle and evolves with the business.
Common Information Security Policy Pitfalls
Many organisations have an information security policy on paper, yet it fails to serve its purpose. A few recurring problems are to blame.
- Vague language
A policy that simply promises an appropriate level of security gives no one anything to act on or to check against. - No connection to real business processes
A document written in isolation from day-to-day operations quickly ends up on a shelf and is never consulted. - Lack of leadership buy-in
The board may formally approve the policy, but unless it backs that approval with budget and actively enforces compliance, the document remains a statement of intent. - Objectives that are too broad
Policy objectives need to be specific enough to track. Useful indicators include incident response time and the percentage of staff who have completed security training.

Final Thoughts
An information security policy is the starting point for building an ISMS and bringing structure to the way an organisation protects its data. It bridges regulatory requirements and business strategy, defines who is responsible for what, and ties the remaining security procedures together. As the cornerstone of an information security management system, it needs leadership commitment from the outset and regular reviews to stay in step with the business.
Keeping the policy current and managing the surrounding documentation gets harder as the organisation grows. ISMS software can automate review cycles, assign responsibilities, and generate audit-ready reports. Dedicated ISMS management software makes it easy to version the document, distribute it to staff, and confirm that everyone has read it. Tools like these keep ISMS management practical at any scale.
