Implementing ISO 22301 is one of those tasks that organisations tend to either overcomplicate or underestimate. Some turn it into a months-long initiative involving external consultants and hundreds of pages of documentation. Others assume a handful of contingency plans will do. Neither approach leads to a system that actually works in a crisis and stands up to audit scrutiny. This article takes a practical look at the process, step by step.
What Is ISO 22301?
ISO 22301 defines what a business continuity management system (BCMS) needs to include. At its core, the standard calls for a business impact analysis, documented continuity plans, and regular testing. It stays neutral on tools and technology, which is why it works just as well for a 50-person company as for a large financial institution. Crucially, a BCMS is never finished. Every audit and every test should produce findings that feed back into the system.
Why Business Continuity Management Matters
Disruptions do not wait for organisations to be ready. A data centre goes down, a key supplier disappears, or a cyberattack takes out the IT estate. Without a structured approach to continuity, the response is improvised, downtime drags on, and losses mount.
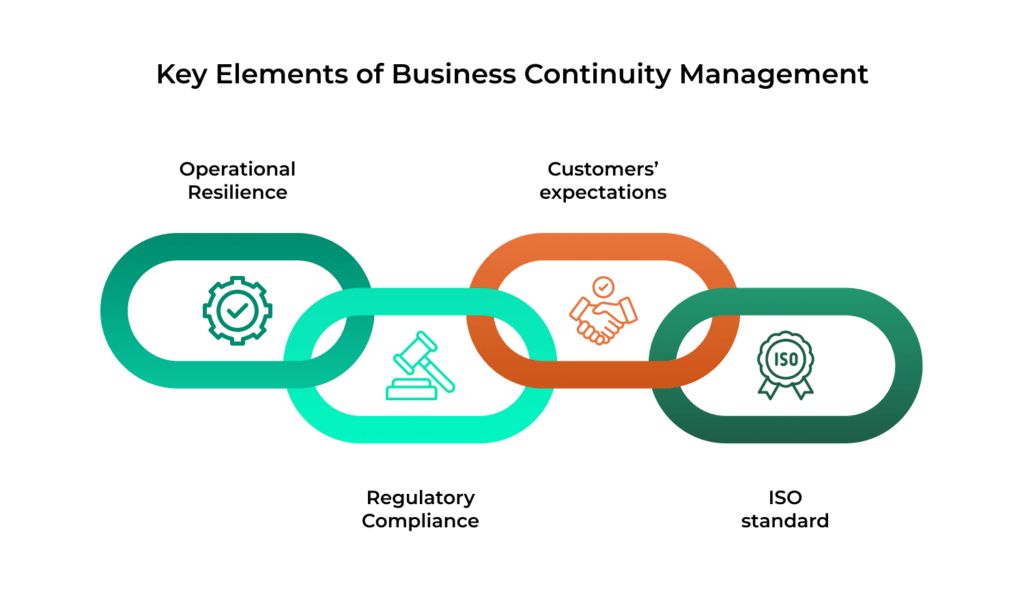
Regulation is raising the bar. The NIS2 Directive requires essential and important entities to have continuity measures in place. DORA sets equivalent expectations for financial institutions around digital operational resilience. Under both regimes, having plans on paper is not enough. Organisations need to show that those plans are tested and kept current.
Commercial pressure is growing too. Large clients in regulated sectors increasingly expect their suppliers to demonstrate formal business continuity management. An ISO 22301 certificate is one of the clearest ways to do that. And for organisations that already have some of the pieces in place, such as backup procedures, escalation protocols, or ad-hoc recovery plans, the standard offers a way to connect those scattered elements into something coherent.
ISO 22301 and BCM: How They Relate
Business continuity management (BCM) can be approached in two ways. The first is informal: an organisation builds its continuity system independently, choosing its own methods and scope. This gives considerable flexibility, but makes it harder to demonstrate to an auditor or regulator that the system is complete and effective.
The second approach is to build BCM on the foundation of ISO 22301. The standard does not change what business continuity management is, it simply gives it a formal structure, specifying what a system must contain and how to show that it actually works.
The Structure of ISO 22301
The standard has ten clauses. The first three deal with scope and terminology. The actual requirements start at Clause 4.
Clause 4 is about context: the operating environment, interested parties, and the intended scope of the BCMS. Clause 5 covers leadership, including formal approval of a continuity policy and the commitment of resources. Clause 6 addresses planning: identifying risks and opportunities, and setting objectives. Clause 7 is about support, from team competence and staff awareness through to documentation.
The operational heart of the standard sits in Clauses 8 through 10. Clause 8 covers business impact analysis, risk assessment, continuity strategies, and the continuity plans themselves. Clause 9 brings in monitoring, internal audits, and management reviews. Clause 10 closes the loop with corrective actions and continual improvement.
Together, these clauses map onto the PDCA cycle (Plan-Do-Check-Act). Clauses 4 to 7 are the planning phase, Clause 8 is execution, Clause 9 is review, and Clause 10 is improvement. This is what keeps a BCMS alive: it evolves after every test, every audit, and every real incident.
Business Impact Analysis (BIA)
The BIA is the starting point for building continuity plans. It begins with an inventory of the organisation’s assets (business processes, IT systems, personnel, locations, and third-party suppliers) and assesses the consequences of each becoming unavailable. Those consequences may be financial (lost revenue, contractual penalties), regulatory (breach of obligations to a supervisory authority), or operational (production halted, customers unable to be served). From this, the organisation determines which assets and processes are critical and in what order they require protection.
Once the critical processes are identified, the BIA assigns each one several parameters. The Maximum Tolerable Period of Disruption (MTPD) is the longest a process can be unavailable before the damage becomes unacceptable. The Minimum Business Continuity Objective (MBCO) is the lowest level of service at which the organisation can still function. From the MTPD comes the Recovery Time Objective (RTO), the target time for actually getting the process back up. The RTO needs to be shorter than the MTPD to leave room for activating contingency procedures. For IT systems, there is also the Recovery Point Objective (RPO), which sets the maximum tolerable data loss in terms of time and drives backup frequency.
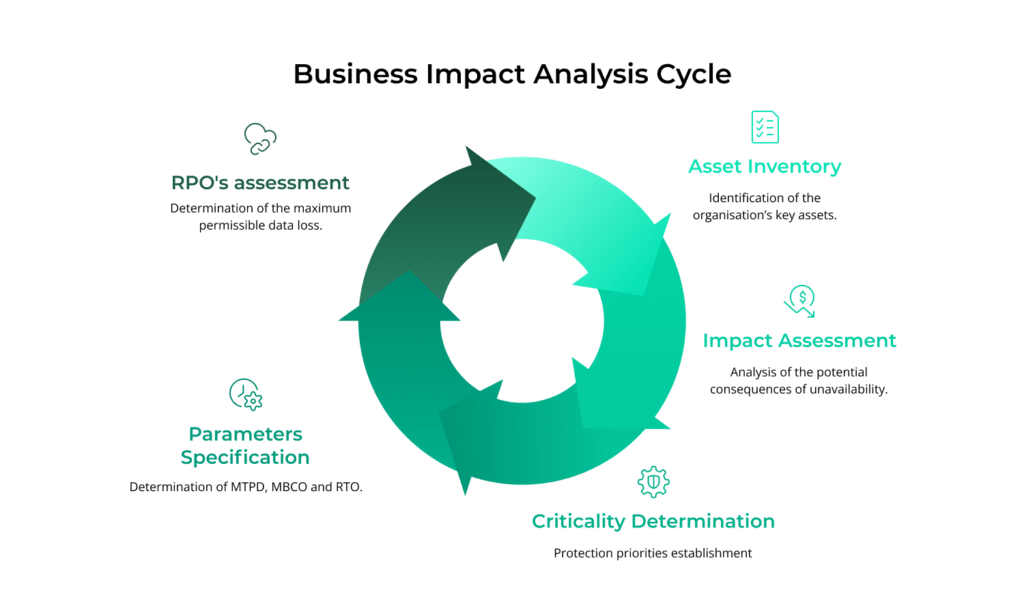
Getting the BIA right means involving the people who own the processes, not just the IT department. Sales, logistics, finance, and customer service teams understand the real consequences of downtime in their areas and the dependencies that link their processes to the rest of the business. The BIA results then feed directly into risk assessment and strategy development.
Risk Assessment in the Context of Business Continuity
The BIA tells you which processes matter most and how quickly they need to come back. Risk assessment asks a different question: what could knock them out, and how likely is that to happen?
The range of threats is broad, and spans IT infrastructure failure, fire, loss of a critical supplier, a cyberattack, or a pandemic. For each one, the task is to gauge both likelihood and potential impact on the processes flagged in the BIA. The outcome is a prioritised view of which risks demand action and which can be accepted.
This kind of risk assessment is different from the one carried out under ISO 27001 for information security. ISO 27001 starts from information assets and threats to their confidentiality, integrity, and availability. ISO 22301 starts from business processes and their ability to keep running regardless of what goes wrong. The two can feed into each other, but they serve different purposes and lead to different decisions.
Continuity Strategies and Business Continuity Plans (BCP)
With the BIA and risk assessment complete, the next step is to decide how to keep critical processes running, or get them back quickly, when something goes wrong.
Strategies vary by area. For IT, that might mean a secondary data centre or a shift to cloud hosting. For people, it means identifying and training deputies for key roles and making remote working viable. For supply chains, it could involve qualifying alternative suppliers or holding buffer stock. Each strategy should tie back to specific processes and to the recovery parameters set in the BIA, particularly MTPD and RTO.
These strategies are then documented in business continuity plans (BCPs). A BCP is a practical, operational document. It spells out who does what during a crisis, in what order, and with what resources. A good BCP also covers communication, both internal and external: who gets notified, when, and how. The more concrete the plan, the less room there is for confusion when it matters most.
Testing and Maintaining the BCMS
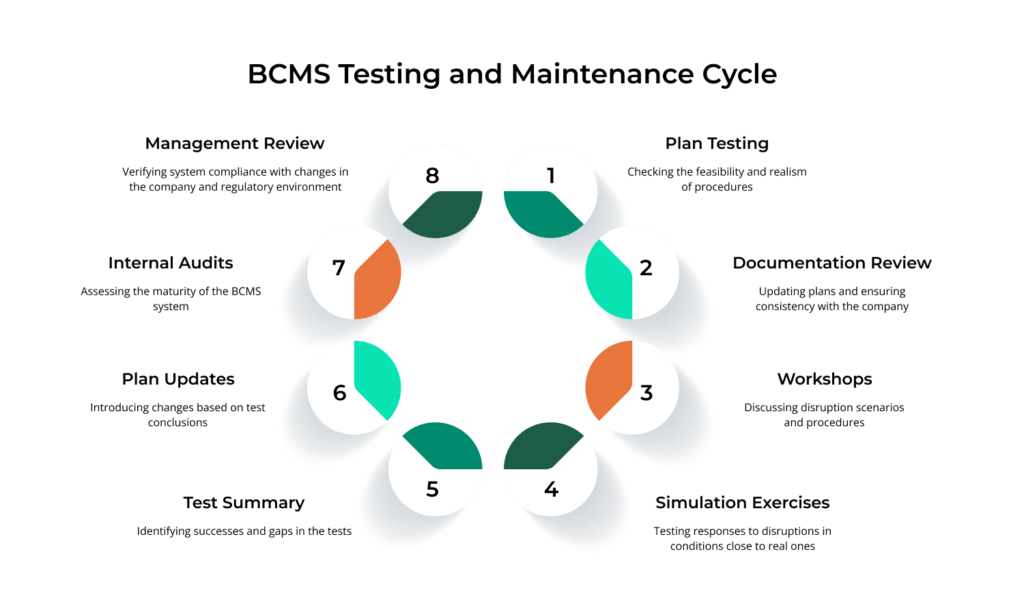
An untested continuity plan is a liability dressed up as reassurance. Only testing reveals whether procedures actually work, whether the team knows its role, and whether the recovery times assumed in the BIA are realistic.
ISO 22301 requires regular testing but leaves the method open. A documentation review is the simplest option, checking that plans reflect the current organisational structure. Tabletop exercises take it further. The team walks through a disruption scenario and discusses the response without actually triggering anything. Full simulation exercises are the most rigorous, testing the real response under conditions close to an actual event.
What matters as much as the test itself is the debrief. What went to plan? What needed improvisation? Where were the gaps? Those findings drive the next round of updates and feed into the PDCA cycle. The standard also calls for internal audits and management reviews, which look at the health of the BCMS as a whole rather than just individual plans. Management reviews sit with senior leadership and should confirm that the system is keeping pace with changes in the business and its regulatory environment.
Integrating ISO 22301 With Other ISO Standards
Plenty of organisations that take on ISO 22301 already run an information security management system under ISO 27001 or follow ISO 31000 for risk management. These standards lend themselves to integration, which cuts down on duplicate documentation and parallel processes.
The integration is straightforward because ISO 22301 and ISO 27001 share the same clause structure, known as the High-Level Structure (HLS). Requirements around context, leadership, planning, internal audits, and improvement follow the same layout in both standards. If an organisation has already been through ISO 27001 implementation, it will have elements that can be extended rather than rebuilt: a leadership-approved policy, internal audit procedures, a management review cycle, and a risk register.
The two standards also complement each other in substance. ISO 27001 is focused on protecting the confidentiality, integrity, and availability of information. ISO 22301 looks more broadly at the ability to sustain critical business processes regardless of the type of disruption. An information security risk assessment will not replace a BIA, but it can supply useful data on IT-related threats worth factoring into continuity planning.
ISO 31000 sits alongside both as a general risk management framework. It is not certifiable, but its principles can help unify the way risk is assessed and managed across the organisation.
Benefits and Good Practices for Implementation
A well-implemented BCMS delivers clear benefits. It strengthens operational resilience by forcing a disciplined approach to identifying threats and preparing for them. An organisation that has been through a proper BIA, built out its continuity strategies, and tested its plans will handle disruptions faster and more predictably.
A formal BCMS also simplifies regulatory compliance. Both NIS2 and DORA expect documented business continuity management, and a system built around ISO 22301 produces exactly the kind of evidence regulators look for. Certification can also matter commercially, especially when a prospective client needs assurance that a supplier can weather disruptions.
On the practical side, three things make the biggest difference. Keep the scope realistic. Start with the processes that genuinely matter and expand from there. Build the BIA and the plans with the people who actually run the processes, not in a back office. And commit to ongoing testing. A BCMS that sits untouched after go-live loses relevance fast. The organisation changes, and plans that are not exercised fall behind.
