Information Security Management System
Centralised activities, process oversight, and compliance with ISO standards.
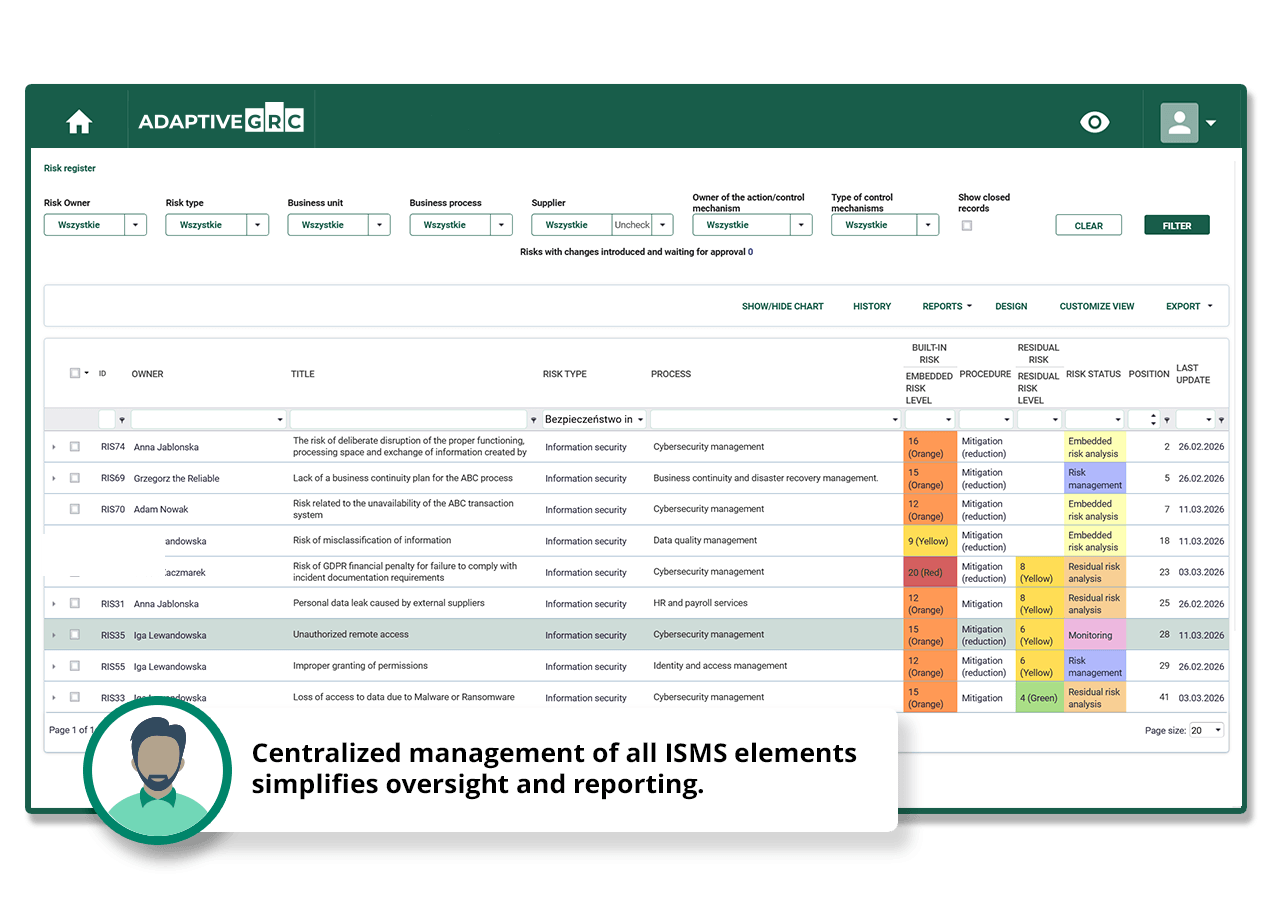
Full control over information security
Gain real control over information security by centralising all ISMS elements within a single, cohesive system. Instead of scattered files, spreadsheets, and emails, you have a single source of truth that simplifies oversight, accelerates reporting, and increases transparency. Built-in risk management mechanisms support you at every stage—from identifying and assessing threats to continuously monitoring them. As a result, you can make informed decisions faster, minimize the risk of incidents, and strengthen your organisation’s resilience to threats.
Contact UsKey AdaptiveGRC functionalities in the Information Security Management System area
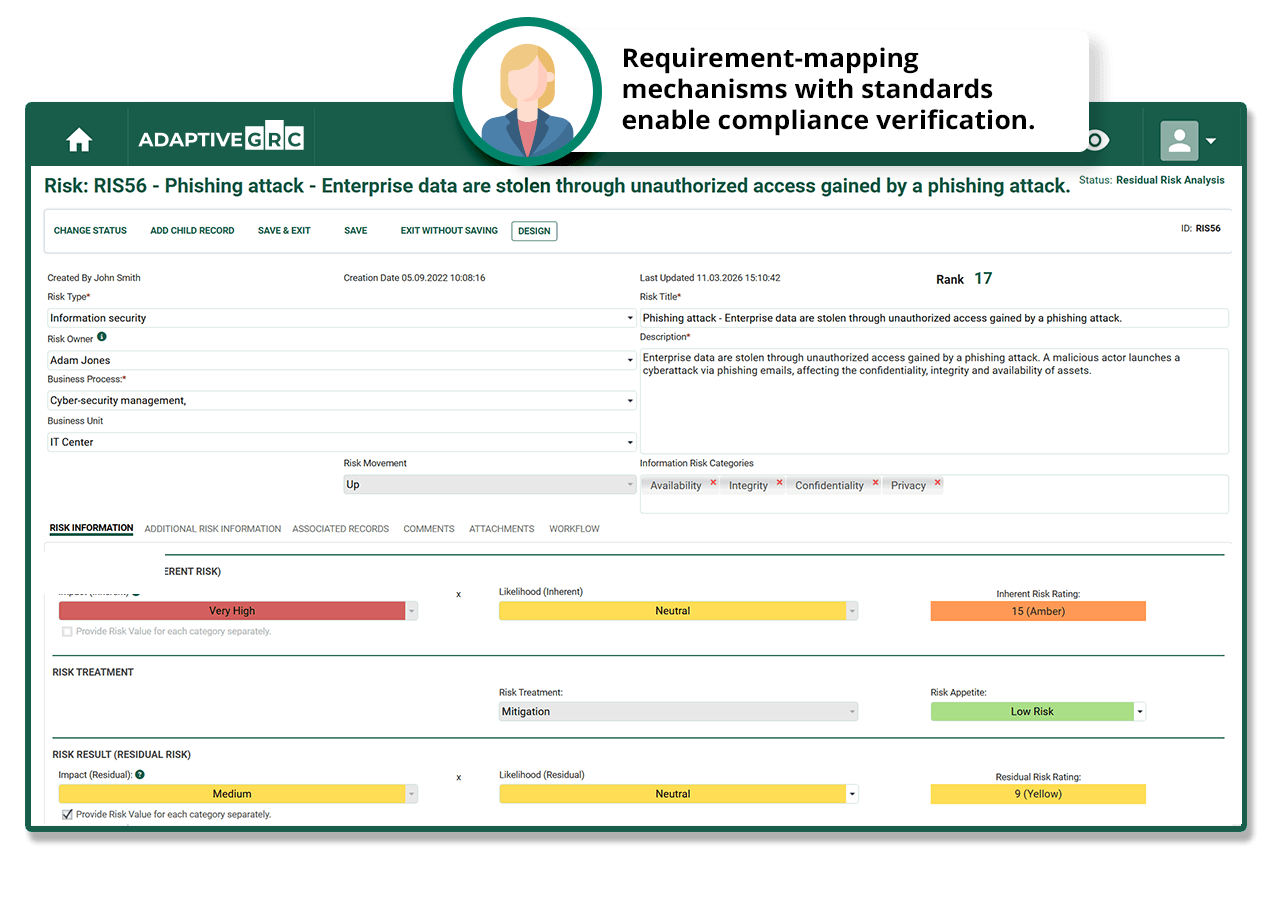
Risk Management
Enables quick assessment of threats and continuous monitoring of risks within the organization. Risk registers, treatment plans, and exposure visualization provide a clear overview of the situation.
Information Asset Register
Allows identification and classification of all information assets within the organization. This makes it easier to manage security and prioritize protection within the BCM framework.
Security Controls Management
Enables assigning and monitoring controls as well as reporting on their effectiveness. This helps maintain a high level of security across the organization.
Incident Management
Allows you to register incidents, analyse their root causes, and implement corrective actions. This helps you respond faster and minimize the impact of security events.
Audit and Compliance
The system supports planning audits of processes and areas related to information security. It enables effective verification of compliance and identification of areas requiring improvement.
Compliance Management
Checklists and reports allow you to verify compliance with standards such as ISO 27001. This makes processes more transparent and maintaining standards easier.
Reporting and Dashboards
Interactive dashboards visualize the state of security and the status of compliance. This allows you to quickly identify key areas that require attention.
Documentation Management
All policies, procedures, and instructions are stored in a single repository. Workflows aligned with the PDCA cycle ensure that processes are structured and easier to monitor.
Application Register
A structured inventory of all applications, including information about owners, criticality levels, and associated risks. This makes it easier to manage system security and monitor compliance with requirements.
Trusted by:


























Compliance and automation – less work, greater confidence
Ensure full compliance with standards such as ISO 27001 through built-in requirement mapping mechanisms and support for audits and second-line control activities. AdaptiveGRC automates repetitive tasks related to controls, audits, and reporting, saving time while minimising the risk of errors. As a result, your processes become more consistent, audits easier, and regulatory compliance fully under control.
Contact UsWe are a global team of passionate people who combine our business and process insights with our technical expertise to develop state-of-the-art business technology solutions.
20+
More than two decades of experience in serving world's largest companies
60+
Programs & projects executed in more than 60 countries all over the globe
420+
Highly skilled and qualified professionals, having both technology and business processes knowledge
500
Organizations listed in Fortune 500 choose us

The AdaptiveGRC platform offers a variety of modules to help manage GRC activities for your company in agreement with the latest regulations (DORA, NIS2).
Streamline Your GRC Activities with AdaptiveGRC
Get Results Faster.
- Fill out the form.
- Our consultant will work with you to determine what your company needs.
- We will schedule a product demo to show you the required features.
- We will gain your feedback and tailor a tool to your needs.